KeyNote is a simple and flexible trust-management system designed to work well for applications.. #Trust-management system #Internet-based applications #Key note #Key #Note #Applications
KeyNote is a simple and flexible trust-management system designed to work well for applications.
Trust management, introduced in the PolicyMaker system [BFL96], is a unified approach to specifying and interpreting security policies, credentials, and relationships; it allows direct authorization of security-critical actions. A trust-management system provides standard, general-purpose mechanisms for specifying application security policies and credentials. Trust-management credentials describe a specific delegation of trust and subsume the role of public key certificates; unlike traditional certificates, which bind keys to names, credentials can bind keys directly to the authorization to perform specific tasks.
A language for describing `actions', which are operations with security consequences that are to be controlled by the system. A mechanism for identifying `principals', which are entities that can be authorized to perform actions. A language for specifying application `policies', which govern the actions that principals are authorized to perform. A language for specifying `credentials', which allow principals to delegate authorization to other principals. A `compliance checker', which provides a service to applications for determining how an action requested by principals should be handled, given a policy and a set of credentials.
The trust-management approach has a number of advantages over other mechanisms for specifying and controlling authorization, especially when security policy is distributed over a network or is otherwise decentralized.
Trust management unifies the notions of security policy, credentials, access control, and authorization. An application that uses a trust- management system can simply ask the compliance checker whether a requested action should be allowed. Policies and credentials are written in standard languages that are shared by all trust-managed applications; the security configuration mechanism for one application carries exactly the same syntactic and semantic structure as that of another, even when the semantics of the applications themselves are quite different.
Trust-management policies are easy to distribute across networks, helping to avoid the need for application-specific distributed policy configuration mechanisms, access control lists, and certificate parsers and interpreters.
For a general discussion of the use of trust management in distributed system security, see [Bla99].
KeyNote is a simple and flexible trust-management system designed to work well for a variety of large- and small- scale Internet-based applications. It provides a single, unified language for both local policies and credentials. KeyNote policies and credentials, called `assertions', contain predicates that describe the trusted actions permitted by the holders of specific public keys. KeyNote assertions are essentially small, highly-structured programs. A signed assertion, which can be sent over an untrusted network, is also called a `credential assertion'. Credential assertions, which also serve the role of certificates, have the same syntax as policy assertions but are also signed by the principal delegating the trust.
In KeyNote:
Actions are specified as a collection of name-value pairs. Principal names can be any convenient string and can directly represent cryptographic public keys. The same language is used for both policies and credentials. The policy and credential language is concise, highly expressive, human readable and writable, and compatible with a variety of storage and transmission media, including electronic mail. The compliance checker returns an application-configured `policy compliance value' that describes how a request should be handled by the application. Policy compliance values are always positively derived from policy and credentials, facilitating analysis of KeyNote-based systems. Compliance checking is efficient enough for high-performance and real-time applications.
This document describes the KeyNote policy and credential assertion language, the structure of KeyNote action descriptions, and the KeyNote model of computation.
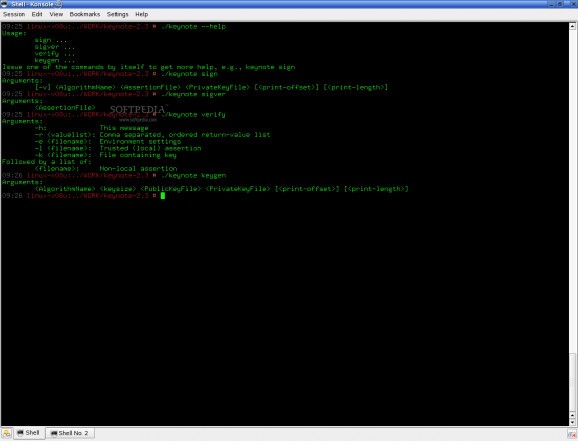
KeyNote 2.3
add to watchlist add to download basket send us an update REPORT- runs on:
- Linux
- filename:
- keynote.tar.gz
- main category:
- System
- developer:
- visit homepage
calibre 7.9.0
Windows Sandbox Launcher 1.0.0
Zoom Client 6.0.3.37634
4k Video Downloader 1.5.3.0080 Plus / 4.30.0.5655
Microsoft Teams 24060.3102.2733.5911 Home / 1.7.00.7956 Work
Bitdefender Antivirus Free 27.0.35.146
ShareX 16.0.1
IrfanView 4.67
7-Zip 23.01 / 24.04 Beta
Context Menu Manager 3.3.3.1
- IrfanView
- 7-Zip
- Context Menu Manager
- calibre
- Windows Sandbox Launcher
- Zoom Client
- 4k Video Downloader
- Microsoft Teams
- Bitdefender Antivirus Free
- ShareX