A Xen-based Linux distribution the provides strong security for desktop computing. #Xen distribution #Linux distribution #Operating system #Xen #Linux #Distribution
Qubes OS is an open source distribution of Linux built around the Xen hypervisor, the X Window System and Linux kernel open source technologies. It is based on Fedora Linux and designed from the ground up to provide users with strong security for desktop computing.
The distribution has been engineered to run almost all Linux applications and uses all of the drivers implemented in the Linux kernel to automatically detect and configure most hardware components (new and old).
Key features include a secure bare-metal hypervisor powered by the Xen project, secure system boot, support for Windows-based and Linux-based AppVMs (Application Virtual Machines), as well as centralized updates for all AppVMs that are based on the same template.
In order to sandbox several core components and isolate certain applications from each other, Qubes OS uses virtualization technology. The integrity of the rest of the system will not be compromised.
It is distributed as a single Live DVD ISO image, supporting only the 64-bit (x86_64) hardware platform, which can be deployed to a USB flash drive or 4GB or bigger, as well as burned onto a DVD disc. From the boot menu, users can try or install the operating system.
The installation process is text-based and allows users to set a timezone, choose the installation source, select software packages to be installed, select the installation destination, set the root password, and create users.
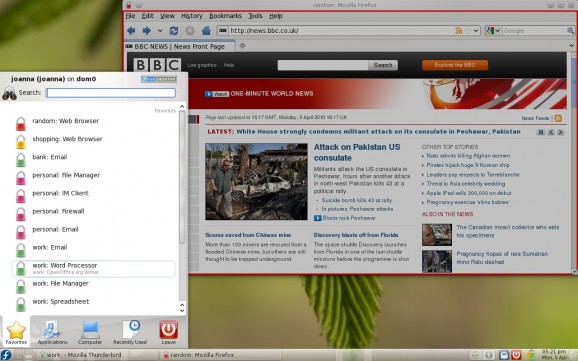
The default desktop environment is powered by the KDE Plasma Workspaces and Applications project, which comprises of a single taskbar located on the upper part of the screen, from where users can access the main menu, launch apps, and interact with running programs.
In conclusion, Qubes OS is a unique Fedora-based operating system that implements a "security by isolation" approach and uses lightweight virtual machines called AppVMs that are definable by users.
What's new in Qubes OS 4.0.2:
- All 4.0 dom0 updates to date
- Fedora 30 TemplateVM
- Debian 10 TemplateVM
- Whonix 15 Gateway and Workstation TemplateVMs
Qubes OS 4.0.2 / 4.0.3 RC1
add to watchlist add to download basket send us an update REPORT- runs on:
- Linux
- filename:
- Qubes-R4.0.2-x86_64.iso
- main category:
- Linux Distributions
- developer:
- visit homepage
IrfanView 4.67
Context Menu Manager 3.3.3.1
4k Video Downloader 1.5.3.0080 Plus / 4.30.0.5655
Windows Sandbox Launcher 1.0.0
Microsoft Teams 24060.3102.2733.5911 Home / 1.7.00.7956 Work
Bitdefender Antivirus Free 27.0.35.146
ShareX 16.0.1
7-Zip 23.01 / 24.04 Beta
calibre 7.9.0
Zoom Client 6.0.3.37634
- 7-Zip
- calibre
- Zoom Client
- IrfanView
- Context Menu Manager
- 4k Video Downloader
- Windows Sandbox Launcher
- Microsoft Teams
- Bitdefender Antivirus Free
- ShareX