A security-enhanced operating system based on open-source with Linux and GNU software. #Linux distribution #Operating system #UNIX distro #Openwall #Linux #Distribution
Openwall GNU/*/Linux (also known as Owl) is an independent, open source and completely free operating system that has been designed from the ground up to bring security into open environments. It’s suitable for servers, as well as virtual and physical appliances.
Anyone can download Openwall GNU/*/Linux for free, as it is distributed as Live DVD ISO image of approximately 1GB in size, archived with the GZ compression algorithm resulting in files that are half the size than that of the ISO image.
The operating system features a minimal boot menu that allows the user to only start the live and installable system in normal or safe modes by pressing the Enter key on a highlighted boot option.
Experienced Linux users can press Tab on a selected boot entry to edit its options and start an existing operating system that is installed on a local drive for rescue purposes only.
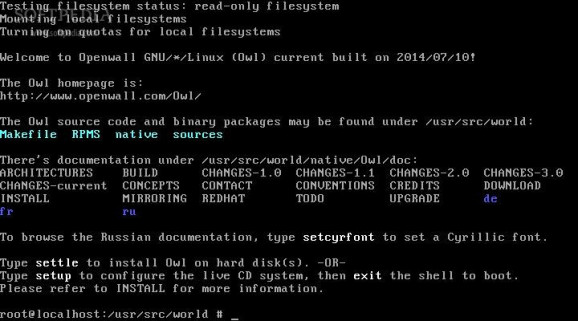
Despite the fact that the Live DVDs have approximately 1GB in size, the OS has no graphical desktop environment. It will drop users to a shell prompt where they must use the “settle” command to install the distro or the “setup” command to configure the live system, then exit the shell to boot.
The Openwall GNU/*/Linux setup script will allow you to configure localization, set the root (system administrator) password, select a timezone, configure the network and run the shell.
All things considered, Openwall GNU/*/Linux is a command-line, secure and minimal operating system that features remote SSH access. It is based used for deploying dedicated servers, but also to rescue broken OSes or install Linux distributions.
What's new in Openwall GNU/*/Linux 3.1:
- Recent changes in Owl 3.1-stable include update to RHEL 5.11-based Linux/OpenVZ kernel along with Red Hat's fix for a local privilege escalation vulnerability on x86-64 (CVE-2014-9322). So please upgrade.
Openwall GNU/*/Linux 3.1-20160824
add to watchlist add to download basket send us an update REPORT- runs on:
- Linux
- filename:
- Owl-3_1-stable-20160824-x86_64.iso.gz
- main category:
- Linux Distributions
- developer:
- visit homepage
IrfanView 4.67
Zoom Client 6.0.0.37205
Windows Sandbox Launcher 1.0.0
Bitdefender Antivirus Free 27.0.35.146
7-Zip 23.01 / 24.04 Beta
calibre 7.9.0
Microsoft Teams 24060.3102.2733.5911 Home / 1.7.00.7956 Work
4k Video Downloader 1.5.3.0080 Plus / 4.30.0.5655
ShareX 16.0.1
paint.net 5.0.13 (5.13.8830.42291)
- 4k Video Downloader
- ShareX
- paint.net
- IrfanView
- Zoom Client
- Windows Sandbox Launcher
- Bitdefender Antivirus Free
- 7-Zip
- calibre
- Microsoft Teams