A set of free software userspace tools for Linux that allow system administrators to interact with the Connection Tracking System.. #Connection tracking #Connection monitoring #Network #Connection #Tracking #Monitoring
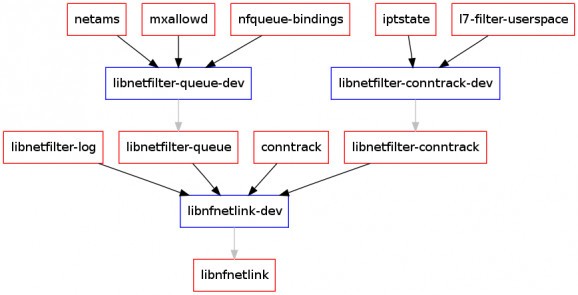
conntrack-tools offers a set of free software userspace tools for Linux that allow system administrators to interact with the Connection Tracking System, which is the module that provides stateful packet inspection for iptables. The conntrack-tools are the userspace daemon conntrackd and the command line interface conntrack.
The userspace daemon conntrackd can be used to enable high availability cluster-based stateful firewalls and collect statistics of the stateful firewall use. The command line interface conntrack provides a more flexible interface to the connnection tracking system than /proc/net/ip_conntrack.
Lots of cool things. conntrackd covers the specific aspects of stateful Linux firewalls to enable high availability solutions and it can be used as statistics collector of the firewall use as well. The command line interface conntrack provides an interface to add, delete and update flow entries, list current active flows in plain text/XML, current IPv4 NAT'ed flows, reset counters atomically, flush the connection tracking table and monitor connection tracking events among many other.
Yes. conntrackd synchronizes the states among several replica firewalls, so you can deploy failover setups with stateful Linux firewalls. See the support section for more information. However, conntrackd can be also used to collect statistics of the stateful firewall use.
There are several good reasons to do so. The /proc interface offers a quite limited interface to the Connection Tracking System since it only allows you to dump current active network flows. Instead, conntrack allows you to update network flows without adding a new iptables rule, e.g. update the conntrack mark, or dump the connection tracking table in XML format. Moreover, using the /proc interface to dump the connection tracking table under very busy firewalls, i.e. those with tons of connection states, harms performance. Specifically, this becomes a problem if you poll from the /proc interface to get firewall statistics. Also, conntrack offers connection events monitoring which a feature that the /proc interface does not provide.
Yes. You can use conntrack to kill an established TCP connection without adding an iptables rule. Of course, you require a sane stateful ruleset which would block a packet that does not match any existing entry in the Connection Tracking Table. Basically, the idea consists of removing the entry that talks about the victim TCP connection. Thus, the client experiences a connection hang. Moreover, since conntrack is not dependent of the layer 4 protocol, you can use to kill whatever layer 4 network flow (UDP, SCTP, ...).
What's new in conntrack-tools 1.4.1:
- This version adds support to dump the "dying" and "unconfirmed" list via ctnetlink.
- A deadlock due to wrong nested signal blocking was resolved.
conntrack-tools 1.4.1
add to watchlist add to download basket send us an update REPORT- runs on:
- Linux
- main category:
- System
- developer:
- visit homepage
Zoom Client 6.0.3.37634
Bitdefender Antivirus Free 27.0.35.146
Context Menu Manager 3.3.3.1
Windows Sandbox Launcher 1.0.0
Microsoft Teams 24060.3102.2733.5911 Home / 1.7.00.7956 Work
ShareX 16.0.1
7-Zip 23.01 / 24.04 Beta
IrfanView 4.67
4k Video Downloader 1.5.3.0080 Plus / 4.30.0.5655
calibre 7.9.0
- IrfanView
- 4k Video Downloader
- calibre
- Zoom Client
- Bitdefender Antivirus Free
- Context Menu Manager
- Windows Sandbox Launcher
- Microsoft Teams
- ShareX
- 7-Zip