Viper is a brute-force password cracker.. #Password cracker #Password hashes #Password strings #Brute-force #Password #Cracker
Viper is a brute-force password cracker.
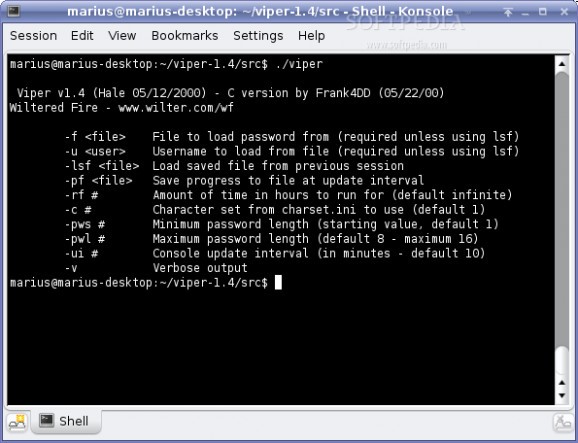
When I was trying to understand the insecurity of UNIX passwords, I looked for simple password cracking software as an example. Sure, there was the famous Crack, but I found Hale's viper.pl more readable. I wanted to improve the code to measure and print performance and time estimates for brute force attacks, so I contacted Hale about my ideas including re-writing his program in 'C' for maximum speed.
I wanted to know how long it takes to check for every possible password combination on different computing platforms, for different character sets and for different password lengths. The results were highly interesting!
But first, we need to look into more details how passwords work and how they are generated. After that, writing a password cracker is not that hard. The basic design of a brute-force password cracker is a loop in which we continuously compute password hashes from incremented password strings of a generic character set - and compare the result to the real password hash until they match. Lets assume the password just contains lowercase letters from 'a' through 'z', we would start hashing and comparing:
'a', 'b', 'c', 'd'... 'w', 'x', 'y', 'z', then 'aa', 'ab', 'ac', 'ad' ... 'zw', 'zx', 'zy', 'zz', then 'aaa', 'aab', 'aac', 'aad' ... 'zzw', 'zzx', 'zzy', 'zzz' ... continuing to the maximum password length until we find the 'winning' combination. The faster it runs the better, because simple math tells us how many password string combinations we need to check. Using the example of a password with max. 8 characters (all lower case), we can calculate the total number of combinations (example for the 26 lowercase letters of the English alphabet):
(26)+ 261+ (26x26)+ 262+ (26x26x26)+ 263+ (26x26x26x26)+ 264+ (26x26x26x26x26)+ 265+ (26x26x26x26x26x26)+ 266+ (26x26x26x26x26x26x26)+ 267+ (26x26x26x26x26x26x26x26) 268
= 217,180,147,158 combinations!
Viper 1.4
add to watchlist add to download basket send us an update REPORT- runs on:
- Linux
- filename:
- viper-1.4.tar.gz
- main category:
- Security
- developer:
- visit homepage
IrfanView 4.67
Windows Sandbox Launcher 1.0.0
7-Zip 23.01 / 24.04 Beta
Microsoft Teams 24060.3102.2733.5911 Home / 1.7.00.7956 Work
Bitdefender Antivirus Free 27.0.35.146
Zoom Client 6.0.0.37205
calibre 7.9.0
ShareX 16.0.1
4k Video Downloader 1.5.3.0080 Plus / 4.30.0.5655
paint.net 5.0.13 (5.13.8830.42291)
- ShareX
- 4k Video Downloader
- paint.net
- IrfanView
- Windows Sandbox Launcher
- 7-Zip
- Microsoft Teams
- Bitdefender Antivirus Free
- Zoom Client
- calibre