Raw Fake AP is a program that emulates valid IEEE 802.11 access points using wireless raw injection. #IEEE 802.11 emulator #Wireless raw injection #IEEE 802.11 access points emulation #IEEE 802.11 #Emulator #Wireless
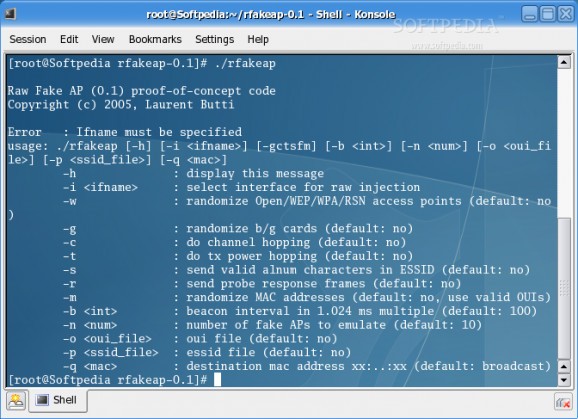
Raw Fake AP is a program that emulates valid IEEE 802.11 access points using wireless raw injection.
Raw Fake AP application aims to create both beacon and probe response frames and could be used to "hide" real networks from novice wardrivers or for testing wireless intrusion detection systems.
Here are some key features of "Raw Fake AP":
Overall features:
� Raw injection of beacon and probe response frames in monitor mode
� Try to forge coherent sequence numbers and BSS timestamps (depending on driver injection capabilities)
� Try to have a coherent time interval between beacons (which is hard to achieve without a real time kernel)
Command line interface will help you to choose between:
� Randomize Open/WEP/WPA/RSN crypto � Randomize b/g cards � Channel hopping � TXpower hopping � Randomize ESSIDs (alnum or not) � Randomize BSSIDs � Choose beacon interval � Choose number of fake access points � Choose a file with valid OUIs � Choose a file with ESSIDs � Choose between beacon or probe response frames � Select a destination MAC address
Requirements:
You basically need:
� A laptop running GNU/Linux � A PCMCIA IEEE 802.11 wireless card � Wireless tools (iwconfig) with channel and txpower support
A raw injection enabled wireless driver (you should check excellent Christophe Devine's aircrack webpage for raw injection hints)
This software was successfully tested on:
� Netgear WG511 (prism54 driver) � Netgear WAG511 (madwifi driver) � Netgear MA401 (hostap driver)
Prism54 and madwifi drivers enable the tool to inject coherent sequence numbers and BSS timestamps.
� make � make install (as root)
What's New in This Release:
� A probe response mode was added.
Raw Fake AP 0.2
add to watchlist add to download basket send us an update REPORT- runs on:
- Linux
- filename:
- rfakeap-0.2.tar.gz
- main category:
- Security
- developer:
- visit homepage
ShareX 16.0.1
Microsoft Teams 24060.3102.2733.5911 Home / 1.7.00.10152 Work
Bitdefender Antivirus Free 27.0.35.146
Context Menu Manager 3.3.3.1
Windows Sandbox Launcher 1.0.0
IrfanView 4.67
7-Zip 23.01 / 24.04 Beta
calibre 7.10.0
Zoom Client 6.0.4.38135
4k Video Downloader 1.6.0.0085 Plus / 4.30.0.5655
- calibre
- Zoom Client
- 4k Video Downloader
- ShareX
- Microsoft Teams
- Bitdefender Antivirus Free
- Context Menu Manager
- Windows Sandbox Launcher
- IrfanView
- 7-Zip