A cross-platform and open source web proxy cache application for Linux and Windows OSes. #Web proxy #Proxy cache #Proxy server #Proxy #Server #Cache
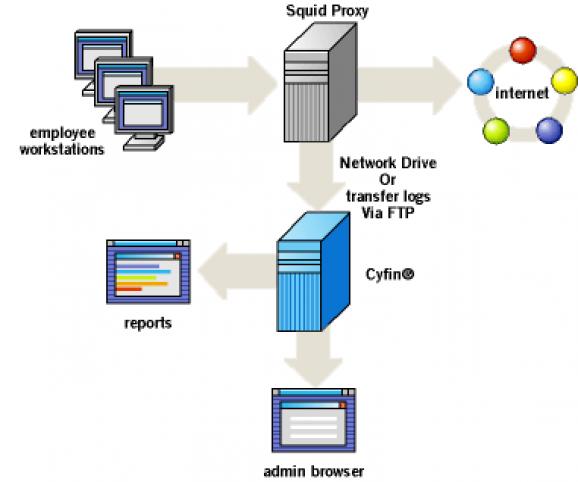
Squid is an open source, full-featured and high-performance web proxy cache application that can be arranged hierarchically for an improvement in response time and a reduction in bandwidth usage.
It works by first caching frequently used websites and then reuse them to provide users with a much faster web browsing experience, as well as to reduce the costs of their expensive Internet plans.
The application supports proxying and caching of the well known HTTP/HTTPS and FTP Internet protocols, as well as other URLs. It supports proxying for SSL (Secure Sockets Layer), cache hierarchies, cache digests, transparent caching, extensive access controls, HTTP server acceleration, and caching of DNS (Domain Name System) lookups.
It supports the ICP (Internet Cache Protocol), HTCP (Hypertext caching protocol), CARP (Common Address Redundancy Protocol), SNMP (Simple Network Management Protocol), and WCCP (Web Cache Communication Protocol) specifications.
The program is mostly used by ISPs (Internet Service Providers) who want to deliver their users with ultra fast and high quality Internet connections, especially for intense web browsing sessions. It is also used by several websites to deliver rich multimedia content faster.
Being the result of many contributions by unpaid and paid volunteers, the Squid project has been successfully tested with popular GNU/Linux distributions, as well as with the Microsoft Windows operating systems.
Squid is an important project for all home Internet users, but it was extremely useful a few years ago when there weren’t so many high-speed Internet Service Providers (ISPs) out there.
These days, thanks to the ever-growing network technologies, one those not need to install and configure a Squid proxy cache server in order to have a faster web browsing experience. However, this doesn’t mean that it’s not useful in some third world countries where high-speed Internet connection is still available only to rich people or big companies.
Squid 4.10
- runs on:
- Linux
- main category:
- Internet
- developer:
- visit homepage
Windows Sandbox Launcher 1.0.0
IrfanView 4.67
calibre 7.9.0
Zoom Client 6.0.3.37634
4k Video Downloader 1.5.3.0080 Plus / 4.30.0.5655
Bitdefender Antivirus Free 27.0.35.146
ShareX 16.0.1
7-Zip 23.01 / 24.04 Beta
Context Menu Manager 3.3.3.1
Microsoft Teams 24060.3102.2733.5911 Home / 1.7.00.7956 Work
- 7-Zip
- Context Menu Manager
- Microsoft Teams
- Windows Sandbox Launcher
- IrfanView
- calibre
- Zoom Client
- 4k Video Downloader
- Bitdefender Antivirus Free
- ShareX